SECURITY BASICS
Authentication is a process in which a user presents a proof of identity to a protected resource so as to exercise his or her assigned access privileges to a computer network, or a server application, or computerized data. In other words, authentication is a process to verify the person who is logging in to a protected system is who he or she claims to be. For instances, a user must present a set of his or her unique username and correct password so as to proof that he or she is genuinely who he or she claims to be, before his or her access to sensitive data is granted.
Authentication is a very critical security component. As a matter of fact, it serves as the first defense line of computer networks. Good authentication prevents unauthorized users from simulating a legitimate user identity.
Generally, there are three user authentication approaches:Something you have, e.g. a key to unlock a door or a token for network access;
Something you know, e.g. passwords or PINs;
Something you are, e.g. biometric authentication such as fingerprints, retina or iris scans, voice recognition, etc.
If any of the above three authentication approach is deployed individually, there are problems. "Something you have" could be stolen; "Something you know" could be guessed, shared, lost, replay or brute-force cracked; "Something you are" is the strongest among these three schemes, but generally the most costly, and may not be appropriate for some user applications due to its complicated nature to user and the need for unique hardwares at user side.
Since problems of single-factor authentications exists, security experts come to two-factor authentication. For instances, token strong authentication combines "Something you have, e.g. token" and "Something you know, e.g. a PIN to activate the token". You need these two-factor to generate a one-time dynamic password with the token so as to perform a secured authentication. Token authentication is recognized as a strong authentication mechanism by security experts.
Two-factor authentication does not only significantly enhances security level but also ensures that any transactions processed by the user cannot be denied and that the user can be held accountable for his actions on the systems. A Digital-Signature to sign transaction is even available to further enhance transactions.
In general, two-factor authentication mechanism should be deployed on higher risks systems such as remote access to networks or offering a financial service through the Internet (e.g. e-banking, online-brokerage, etc.). A number of financial institutions have been offering their e-banking services dependent only on a PIN for security, however, many financial institutions are upgrading their systems by integrating two-factor authentication when offering their services through electronic means.
An effective authentication mechanism should have customer acceptance, ease of use, reliable performance, scalability to accommodate growth, and interoperability with existing systems and strategic plans of the organization.
Authentication is a very critical security component. As a matter of fact, it serves as the first defense line of computer networks. Good authentication prevents unauthorized users from simulating a legitimate user identity.
Generally, there are three user authentication approaches:
If any of the above three authentication approach is deployed individually, there are problems. "Something you have" could be stolen; "Something you know" could be guessed, shared, lost, replay or brute-force cracked; "Something you are" is the strongest among these three schemes, but generally the most costly, and may not be appropriate for some user applications due to its complicated nature to user and the need for unique hardwares at user side.
Since problems of single-factor authentications exists, security experts come to two-factor authentication. For instances, token strong authentication combines "Something you have, e.g. token" and "Something you know, e.g. a PIN to activate the token". You need these two-factor to generate a one-time dynamic password with the token so as to perform a secured authentication. Token authentication is recognized as a strong authentication mechanism by security experts.
Two-factor authentication does not only significantly enhances security level but also ensures that any transactions processed by the user cannot be denied and that the user can be held accountable for his actions on the systems. A Digital-Signature to sign transaction is even available to further enhance transactions.
In general, two-factor authentication mechanism should be deployed on higher risks systems such as remote access to networks or offering a financial service through the Internet (e.g. e-banking, online-brokerage, etc.). A number of financial institutions have been offering their e-banking services dependent only on a PIN for security, however, many financial institutions are upgrading their systems by integrating two-factor authentication when offering their services through electronic means.
An effective authentication mechanism should have customer acceptance, ease of use, reliable performance, scalability to accommodate growth, and interoperability with existing systems and strategic plans of the organization.
STATIC PASSWORD PROBLEM
The most widely implemented authentication is presenting a set of username (so server can reference a user account) and password (so the server can know that the user is the account owner). The username and password are submitted to user database for comparison. If the username and password present by user are same as the set stored in user database, the user is authenticated and access is granted; otherwise, access is denied. Generally speaking, a static password system is used.
This authentication method offers protection and requires no extra investment in technology. For less valuable network resources, such as e-mail, a static password system may probably be sufficient protection.
However, static password is a weak password and hence its implementation is a weak form of authentication. FBI's recent research "National Strategy to Secure Cyberspace" lists weak password is one of the five most common mistakes that leave company and employee data vulnerable. It says that some 40 percent of user password is a weak one.
Static password can be detected by guessing from personal knowledge of the victim's attitudes and interests, unknowingly disclosed to third parties, cracking with freely available hacker tools like brute force cracking software and password reader, dictionary scanning, sniffing a data stream, outright theft, etc. The intrinsic weakness of static password leads to security breaches, for examples, bank fraud, credit card fraud, wired fraud, computer systems failure, etc.
In short, we need two-factor authentication scheme because one factor authentication by itself may not be sufficient to perform authentication that can be relied on.
This authentication method offers protection and requires no extra investment in technology. For less valuable network resources, such as e-mail, a static password system may probably be sufficient protection.
However, static password is a weak password and hence its implementation is a weak form of authentication. FBI's recent research "National Strategy to Secure Cyberspace" lists weak password is one of the five most common mistakes that leave company and employee data vulnerable. It says that some 40 percent of user password is a weak one.
Static password can be detected by guessing from personal knowledge of the victim's attitudes and interests, unknowingly disclosed to third parties, cracking with freely available hacker tools like brute force cracking software and password reader, dictionary scanning, sniffing a data stream, outright theft, etc. The intrinsic weakness of static password leads to security breaches, for examples, bank fraud, credit card fraud, wired fraud, computer systems failure, etc.
In short, we need two-factor authentication scheme because one factor authentication by itself may not be sufficient to perform authentication that can be relied on.
STRONG AUTHENTICATION
For users who need access to more sensitive network resources or to make an online transaction, strong and robust authentication schemes must be deployed to prevent theft or malicious attacks. Security experts Cheswick & Bellovin comment in Firewalls and Internet: "No security expert we know of regards passwords as a strong authentication mechanism. One can achieve a significant increase in security by using one-time passwords."
One option to increase security is to implement two-factor authentication. Two-factor authentication generally refers to systems requiring two authentication factors - something the user knows (such as a PIN) and something the user has (such as a bank ATM card, physical token). Confidence in the security is assured with the knowledge that even if you lose one factor, it would be virtually useless to anyone else unless he or she gets the other factor too.
Increasing the required factors of security from one factor (something the user knows) to two factors (something the user has) or even three factors (something the user is, e.g. biometric such as finger-print, retina, etc) can help in increasing the security level. The more the factors, the higher the security level. From a practical and security equilibrium perspective, security experts claim two-factors authentication is a strong enough solution.
Another means to archive more robust authentication is to implement one-time password, or dynamic password systems that change for each authentication request or in a certain period of time (say every 30 or 60 seconds). One-time password can be used in combination with two-factor authentication.
One option to increase security is to implement two-factor authentication. Two-factor authentication generally refers to systems requiring two authentication factors - something the user knows (such as a PIN) and something the user has (such as a bank ATM card, physical token). Confidence in the security is assured with the knowledge that even if you lose one factor, it would be virtually useless to anyone else unless he or she gets the other factor too.
Increasing the required factors of security from one factor (something the user knows) to two factors (something the user has) or even three factors (something the user is, e.g. biometric such as finger-print, retina, etc) can help in increasing the security level. The more the factors, the higher the security level. From a practical and security equilibrium perspective, security experts claim two-factors authentication is a strong enough solution.
Another means to archive more robust authentication is to implement one-time password, or dynamic password systems that change for each authentication request or in a certain period of time (say every 30 or 60 seconds). One-time password can be used in combination with two-factor authentication.
TOKEN-BASED AUTHENTICATION
Token is a physical small handheld device, in credit-card or key-holder size, with built-in computer that generates information for the user to use during logon process. Token generates one-time dynamic password that is good for only one logon session. Users enter this one-time password during logon to gain access to a secure system. The token combines two-factor authentication and one-time dynamic password techniques and hence is highly recognized as the most trusted authentication approach.
Software token is also available and it provides much the same functionality as a physical token. It is a software programs that run in a personal computer. Security experts believed that a software token is less secure than a physical token because software system could be more easily compromised.
Token-based authentication is a strong security technique used to identify and authenticate users who are attempting to log in to a protected server, or network, or some other secure systems.
Software token is also available and it provides much the same functionality as a physical token. It is a software programs that run in a personal computer. Security experts believed that a software token is less secure than a physical token because software system could be more easily compromised.
Token-based authentication is a strong security technique used to identify and authenticate users who are attempting to log in to a protected server, or network, or some other secure systems.
TIME-SYNCHRONIZATION
There are two approaches each of the dynamic password methods synchronize what password is correct for a specific user at any given time point: Time-Synchronous and Event-Synchronous authentication.
In Time-Synchronous authentication, a proprietary algorithm is used to calculate the one-time dynamic password takes the exact time the authentication is taking place into computing. Tokens based on Time-Synchronized functions usually display in a LCD the correct password at a given time point and based on an internal real-time clock. After a set time interval, say 36 or 60 seconds, it automatically calculates a new password that is generated by taking the new time point into consideration. Once the dynamic password is send to server in authentication process, the password is revoked and the used password can not be used anymore, and thus called one-time password. This leads to even strong security when token is used in user authentication.
In Time-Synchronous authentication, a proprietary algorithm is used to calculate the one-time dynamic password takes the exact time the authentication is taking place into computing. Tokens based on Time-Synchronized functions usually display in a LCD the correct password at a given time point and based on an internal real-time clock. After a set time interval, say 36 or 60 seconds, it automatically calculates a new password that is generated by taking the new time point into consideration. Once the dynamic password is send to server in authentication process, the password is revoked and the used password can not be used anymore, and thus called one-time password. This leads to even strong security when token is used in user authentication.
EVENT-SYNCHRONIZATION
In Event-Synchronous authentication, the algorithm used to calculate the dynamic password based on an internal event counter takes how many times the user has attempted authentication into computing, instead of taking the current time point.
This is also called Challenge-Response authentication performed by the server sending a challenge code to the user during authentication process, user then keys the challenge into token to compute a correct response, which is the password to the server in this case. Because there is an extra dynamic user input (i.e. challenge code) generated by the authentication server, Challenge-Response authentication is claimed to be even stronger authentication approach; and because only exact server can produce a correct challenge and accept a correct response, it also possess the intrinsic functionality that not only the server is authenticating the user but also the user is authenticating the server simultaneously.
This is also called Challenge-Response authentication performed by the server sending a challenge code to the user during authentication process, user then keys the challenge into token to compute a correct response, which is the password to the server in this case. Because there is an extra dynamic user input (i.e. challenge code) generated by the authentication server, Challenge-Response authentication is claimed to be even stronger authentication approach; and because only exact server can produce a correct challenge and accept a correct response, it also possess the intrinsic functionality that not only the server is authenticating the user but also the user is authenticating the server simultaneously.
TOKEN DIGITAL SIGNATURE
To ensure the integrity of data or information in the transmission process, some tokens even support Digital-Signature (also called Message Authentication Code, MAC in short) that is a digital signing technique to prevent the data or information is not altered and that it is indeed from the person who claims to have sent it. In addition, data or information digitally signed should be non-revocable, i.e. preventing the sender to claim that he or she did not send the data or information. For instances, generating a Digital-Signature based on a specific data parameters and send to server, the Digital-Signature is checked against the database and the data parameters, to determine if the signature is valid.
Hackers could be able to intercept during transmission, but they have no way to alter the data parameters, if they do so then the signature is no longer valid. This ensures the integrity of the contents and is highly secure. Banks or financial institutions especially appreciate this function because this makes sure that their clients' transactions are limited to fraud, non-revocable, and with limited bank liability. This is extremely practical to use Digital Signature in signing transaction, because of data integrity and preventing the signer to refuse that he is not the one who process the transaction.
Hackers could be able to intercept during transmission, but they have no way to alter the data parameters, if they do so then the signature is no longer valid. This ensures the integrity of the contents and is highly secure. Banks or financial institutions especially appreciate this function because this makes sure that their clients' transactions are limited to fraud, non-revocable, and with limited bank liability. This is extremely practical to use Digital Signature in signing transaction, because of data integrity and preventing the signer to refuse that he is not the one who process the transaction.
AUTHENTICATION COMPARISON
Smart-card solution consists of a card reader on client-side. Obviously, disadvantage of this system are costs of setting up and maintaining the card readers in various locations. It is inconvenient in geographical and flexibility perspectives, without claiming that it is less secure due to no real time clock.
Authentication on Internet one-time shopping is another matter because there is no previous contact between the user and the service provider. This requires authentication techniques that use digital certificate.
Authentication on Internet one-time shopping is another matter because there is no previous contact between the user and the service provider. This requires authentication techniques that use digital certificate.
Avoid " Phishing ", use DIGITKEY Strong Authentication
Network Technology and our ever-more-connected society makes globalization faster and easier, but it generates opportunities for thief to steal another's vital information to enrich himself / herself.
Although Congress passed the Identity Theft and Assumption Deterrence Act in 1998, which made identity theft a federal crime subject to as many as 15 years in prison. Still, identity theft flourishes, and one easy and increasingly popular way of capturing personal data is called " Phishing ".
" Phishing " is nothing new, it's a type of hacking technique that has been around for years and in fact predates computers. Malicious crackers did it over the phone for years and called it social engineering. What is new is its contemporary delivery vehicle - spam and faked Web pages.
As of recent cases, there have been an increasing number of internet banking fraud cases, particularly involving fake bank websites and e-mails in order to steal e-banking username and password. Reported cases where consumers are know to have fallen victim to such fraudulent schemes.
Financial Institutions are adviced to implement appropriate security controls for their internet banking services. As any mishaps would undermine the public's confidence in internet banking and would not only be detrimental to the financial institutions' concerned, but also to the development of the e-banking industry as a whole.
Although Congress passed the Identity Theft and Assumption Deterrence Act in 1998, which made identity theft a federal crime subject to as many as 15 years in prison. Still, identity theft flourishes, and one easy and increasingly popular way of capturing personal data is called " Phishing ".
" Phishing " is nothing new, it's a type of hacking technique that has been around for years and in fact predates computers. Malicious crackers did it over the phone for years and called it social engineering. What is new is its contemporary delivery vehicle - spam and faked Web pages.
As of recent cases, there have been an increasing number of internet banking fraud cases, particularly involving fake bank websites and e-mails in order to steal e-banking username and password. Reported cases where consumers are know to have fallen victim to such fraudulent schemes.
Financial Institutions are adviced to implement appropriate security controls for their internet banking services. As any mishaps would undermine the public's confidence in internet banking and would not only be detrimental to the financial institutions' concerned, but also to the development of the e-banking industry as a whole.
What is " Phishing "?
(" Phishing " = FISHing), pp.
Phishing attacks use 'spoofed' e-mails and fraudulent websites designed to fool recipients into divulging personal financial data such as credit card numbers, account usernames and passwords, social security numbers, etc. By hijacking the trusted brands of well-known banks, online retailers and credit card companies, phishers are able to convince up to 5% of recipients to respond to them.
Phishing is a term coined by hackers who imitate legitimate companies in e-mails to entice people to share passwords or credit-card numbers. Phishing comes from the fact that Internet scammers are using increasingly sophisticated lures as they "fish" for Users' financial information and password data.
For more information about Phishing cases and information, please visit Anti-Phishing Working Group at www.anti-phishing.com.
Phishing attacks use 'spoofed' e-mails and fraudulent websites designed to fool recipients into divulging personal financial data such as credit card numbers, account usernames and passwords, social security numbers, etc. By hijacking the trusted brands of well-known banks, online retailers and credit card companies, phishers are able to convince up to 5% of recipients to respond to them.
Phishing is a term coined by hackers who imitate legitimate companies in e-mails to entice people to share passwords or credit-card numbers. Phishing comes from the fact that Internet scammers are using increasingly sophisticated lures as they "fish" for Users' financial information and password data.
For more information about Phishing cases and information, please visit Anti-Phishing Working Group at www.anti-phishing.com.
Phishing Scheme
Recurring patterns
The Fraudster targets Static Passwords, simply because Static Passwords are widely used on Internet accounts for most kinds of business purposes; and Static Passwords can be easily re-used by Fraudster.
Phishing Fraud Scheme
Email containing an invitation to verify or to enter Username and Password is broadcasted from a fake server address, pretending to be the real company or Financial Institution that provides services (for instances, e-Banking, online-brokergae, etc.) to the targeted users. The fake website appears like the real one from the Financial Institution.
A Microsoft Internet Explorer programming code bug is used to display the address of the real website, so as to masking the fake website address. In other words, the characters in the Internet Explorer browser URL are masking the real URL address of the faked website.
The purpose of masking the URL of the faked website is to obtain the Users' authentication information (like username and static password), by sending out massive amount of emails. On the fake, but very real looking and feeling website, the Username & Password are collected by the Fraudster.
In most cases, the gathered pairs of Username & Password can be processed in batch by the Fraudster any time afterwards. This is a batch process, which makes it more manageable, as the Fraudster does not need to wait for Username & Password information to arrive.
The Fraudster targets Static Passwords, simply because Static Passwords are widely used on Internet accounts for most kinds of business purposes; and Static Passwords can be easily re-used by Fraudster.
Phishing Fraud Scheme
Email containing an invitation to verify or to enter Username and Password is broadcasted from a fake server address, pretending to be the real company or Financial Institution that provides services (for instances, e-Banking, online-brokergae, etc.) to the targeted users. The fake website appears like the real one from the Financial Institution.
A Microsoft Internet Explorer programming code bug is used to display the address of the real website, so as to masking the fake website address. In other words, the characters in the Internet Explorer browser URL are masking the real URL address of the faked website.
The purpose of masking the URL of the faked website is to obtain the Users' authentication information (like username and static password), by sending out massive amount of emails. On the fake, but very real looking and feeling website, the Username & Password are collected by the Fraudster.
In most cases, the gathered pairs of Username & Password can be processed in batch by the Fraudster any time afterwards. This is a batch process, which makes it more manageable, as the Fraudster does not need to wait for Username & Password information to arrive.
Anti-Phishing, use DIGITKEY
DIGITKEY family is the utimate security solution to fight Phishing
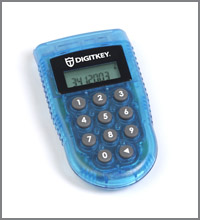
A DIGITKEY is a token solution that generates dynamic One-Time-Password, which changes every 36 seconds, secured by a user-defined PIN code, so as to verify he / she is the genuine user.
The time-based dynamic One-Time-Password is computed using a few parameters: time, unique encryption key, "seed value", application-based parameters, DES / 3-DES encryption algorithm, and even a dynamic Challenge code.
DIGITKEY contains internal real-time clock, which is used as one of parameters for Time-Based password computing.
DIGITKEY solution consist of an authentication server software, which is a C-Library with C-API or Java-wrapper for easy integration into any platforms, on any operating system in any (legacy) software.
Why DIGITKEY solution is secure enough?
The DIGITKEY token generated passwords are unique and secure because of the One-Time and Time-Based Passwords characteristics. Replaying of passwords is denied by authentication server software as the password is expired with time.
Time-Based characteristic forces the Fraudster to operate in (almost) real time. Therefore, Fraudster must sit in between customer and financial institution for communication reasons between both parties. And verify stolen passwords in real time reduces the time for the Fraudster to act, due to expiration of the Password.
One-Time-Password can be used once only. If the password is stolen, it can be used one time only (and must be act fast enough, within the valid period).
Batch processing of Username & Passwords is no longer possible for Fraudster. This puts a time pressure on Fraudster. Moreover, instead of waiting for many passwords to be collected, the Fraudster now has to be present at the moment the Username & Password are revealed, as he has to use this pair immediately and within the valid period.
Where are the One-Time-Passwords situated in the security layers?Authentication (e.g. Static Password, DIGITKEY, Certificates, etc)
Application Security Layer (e.g. DES, 3-DES, AES, etc)
Protocol Layer (e.g. SSL, Tunnels, etc)
Access Security Layer (e.g. Firewalls, Routers, etc)
Networking Security Layer (e.g. VPN, Leased Lines, etc)
Physical Security (e.g. Building door, Fiber protection, etc)
A DIGITKEY is a token solution that generates dynamic One-Time-Password, which changes every 36 seconds, secured by a user-defined PIN code, so as to verify he / she is the genuine user.
The time-based dynamic One-Time-Password is computed using a few parameters: time, unique encryption key, "seed value", application-based parameters, DES / 3-DES encryption algorithm, and even a dynamic Challenge code.
DIGITKEY contains internal real-time clock, which is used as one of parameters for Time-Based password computing.
DIGITKEY solution consist of an authentication server software, which is a C-Library with C-API or Java-wrapper for easy integration into any platforms, on any operating system in any (legacy) software.
Why DIGITKEY solution is secure enough?
The DIGITKEY token generated passwords are unique and secure because of the One-Time and Time-Based Passwords characteristics. Replaying of passwords is denied by authentication server software as the password is expired with time.
Batch processing of Username & Passwords is no longer possible for Fraudster. This puts a time pressure on Fraudster. Moreover, instead of waiting for many passwords to be collected, the Fraudster now has to be present at the moment the Username & Password are revealed, as he has to use this pair immediately and within the valid period.
Where are the One-Time-Passwords situated in the security layers?
How DIGITKEY works?
How does DIGITKEY work?
Every User has a personalized and hence unique DIGITKEY token. The User can generate a Time-Based One-Time-Password with DIGITKEY token. The User enters the dynamic One-Time-Password into the Password field, as re-quested by the Server for authenticate himself / herself. In other words, now the user just login to his / her account using the token generated password, instead of a static password. All the other procedures are just like he/she always does with Username/Password approach.
The authentication server software uses the Username to get data from the Customer database and the real time clock of the System to re-compute the One-Time-Password for this User. The software then verifies both username & the submitted One-Time-Password to authenticate the User.
DIGITKEY TOKEN TYPES
1) DIGITKEY with a PIN: Having a numeric keypad so as for entering the PIN
The PIN has is issued by the financial institution
User has to enter the PIN to activate his / her own token before a dynamic One-Time-Password is gernerated
The PIN is user-changeable
More secure
Supports Challenge/Response & Digital Signature functions
2) DIGITKEY without a PIN:
Smaller size, more convenient to carry
Easier to use and deploy
No PIN issuing procedures (see above)
Less functionalities, as no numeric keypad
DIGITKEY Tokens Optional Functions
1) Time-Based One-Time-Passwords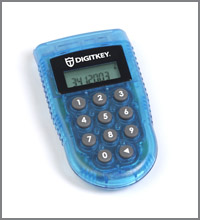
Each password can be used only once
One-Time-Password expires with time
A new password is computed in each 36 seconds
Optional wider time window than 36 seconds of server to accept the dynamic passwords
The wider time-window, the lower the security.
The longer the password, the higher the security.
Combining unknown secrets (seed values), unique encryption key, computing algorithm, verification procedure and real time clock puts the Fraudster under time pressure, and makes DIGITKEY unbeatable in password " Phishing ".
2) Time-Based Challenge/Response
 First we have to understand the procedure of Challenge/Response:
First we have to understand the procedure of Challenge/Response:
Users signs on with User ID only
Server/System returns a Challenge to User
User enters the Challenge to DIGITKEY
DIGITKEY generates a Response
User sends Response to the server
User gets authenticated by the server
Challenge/Response approach is a very complex process for Fraudster. The Fraudster has to use Username immediately to get the appropriate current Challenge from the Server. So he needs to be connected already to the Server/Website. Once he receives the Challenge, he needs to present the Challenge to the Customer. The Customer can then generate a Response to Challenge using his DIGITKEY. After receiving Response from the Customer, the Fraudster could try to make his fraudulent move, as the Response is again time based.
Not only the Fraudster has now to wait for a User to send Username, but the Fraudster now also needs to interact in the communication and in a Real-time mode between User and Financial Institution passing the Challenge and getting the Response.
Challenge/Response authentication approach is even stronger, as there are many steps the Frauster has to react between User & Server in short time, in a single fraud. Moreover, there is an additional dynamic parameter (i.e. the Challenge code) to generate a dynamic Response.
3) DIGITAL SIGNATURE
 Digital Signature is a code generates by DIGITKEY for signing a transaction.
Digital Signature is a code generates by DIGITKEY for signing a transaction.
A Financial Institution can request users to compute a Digital Signature with his / her DIGITKEY if the user wants to excute a transaction or only at important transactions.
This Signature contains unique encrypted data and parameters of the transaction, which can be Account number, Receiving Account Number, Amount, Date, etc.
Moreover this Signature is again Time Based.
If the transaction data is altered by a Fraudster, the server denies the signature code as the Digital Signature needs to change accordingly. This leaves the Fraudster at no chance at all.
4) Host/website authentication
Not only the banks have to authenticate their users, but users need to authenticate if he / she is visiting a authentic website (not faked ones).
DIGITKEY generates a longer Time-Based One Time Password.
Only first part is shown to User on the display of the DIGITKEY for him / her to enter to the bank's logon field.
Bank receives Username & first part Password, then calculates latter part of the Password and display to the user
The User enters latter part of the Password into his /her DIGITKEY
If correct the DIGITKEY will let the User know.
Every User has a personalized and hence unique DIGITKEY token. The User can generate a Time-Based One-Time-Password with DIGITKEY token. The User enters the dynamic One-Time-Password into the Password field, as re-quested by the Server for authenticate himself / herself. In other words, now the user just login to his / her account using the token generated password, instead of a static password. All the other procedures are just like he/she always does with Username/Password approach.
The authentication server software uses the Username to get data from the Customer database and the real time clock of the System to re-compute the One-Time-Password for this User. The software then verifies both username & the submitted One-Time-Password to authenticate the User.
DIGITKEY TOKEN TYPES
1) DIGITKEY with a PIN:
2) DIGITKEY without a PIN:

DIGITKEY Tokens Optional Functions
1) Time-Based One-Time-Passwords
Combining unknown secrets (seed values), unique encryption key, computing algorithm, verification procedure and real time clock puts the Fraudster under time pressure, and makes DIGITKEY unbeatable in password " Phishing ".
2) Time-Based Challenge/Response
 First we have to understand the procedure of Challenge/Response:
First we have to understand the procedure of Challenge/Response:
Challenge/Response approach is a very complex process for Fraudster. The Fraudster has to use Username immediately to get the appropriate current Challenge from the Server. So he needs to be connected already to the Server/Website. Once he receives the Challenge, he needs to present the Challenge to the Customer. The Customer can then generate a Response to Challenge using his DIGITKEY. After receiving Response from the Customer, the Fraudster could try to make his fraudulent move, as the Response is again time based.
Not only the Fraudster has now to wait for a User to send Username, but the Fraudster now also needs to interact in the communication and in a Real-time mode between User and Financial Institution passing the Challenge and getting the Response.
Challenge/Response authentication approach is even stronger, as there are many steps the Frauster has to react between User & Server in short time, in a single fraud. Moreover, there is an additional dynamic parameter (i.e. the Challenge code) to generate a dynamic Response.
3) DIGITAL SIGNATURE
 Digital Signature is a code generates by DIGITKEY for signing a transaction.
Digital Signature is a code generates by DIGITKEY for signing a transaction.
A Financial Institution can request users to compute a Digital Signature with his / her DIGITKEY if the user wants to excute a transaction or only at important transactions.
This Signature contains unique encrypted data and parameters of the transaction, which can be Account number, Receiving Account Number, Amount, Date, etc.
Moreover this Signature is again Time Based.
If the transaction data is altered by a Fraudster, the server denies the signature code as the Digital Signature needs to change accordingly. This leaves the Fraudster at no chance at all.
4) Host/website authentication
Not only the banks have to authenticate their users, but users need to authenticate if he / she is visiting a authentic website (not faked ones).
DIGITKEY generates a longer Time-Based One Time Password.
Only first part is shown to User on the display of the DIGITKEY for him / her to enter to the bank's logon field.
Bank receives Username & first part Password, then calculates latter part of the Password and display to the user
The User enters latter part of the Password into his /her DIGITKEY
If correct the DIGITKEY will let the User know.
DIGITKEY Application Scenarios
1) e-Banking and phone-Banking:
DIGITKEY Strong Authentication is secure solution but not difficult to integrate at all. Thanks to the DIGITKEY Controller server which is a C-Library with C-API or Java-wrapper. It operates on any Operating Systems with any existing server applications. It use your existing Application Client Database. There is no need to upgrade your existing systems at all.
More than 250 Financial Institutions has integrated DIGITKEY Controller for securing e-Banking, phone-banking, e-Brokerage, etc.
2) E-Commerce integration
DIGITKEY authentication solution has already been integrated into 3D-Secure schemes: SecureCode from MasterCard
"Verified By VISA"
By several Market leading Vendors like CYOTA, Element, ARCOT, etc.
3) Remote Access & Corporate Network Access
The DIGITKEY authentication solution has been integrated in Firewalls, VPN, Radius servers, Portal softwares, ... from many Vendors: Netscreen, Lucent Technologies, Stonesoft, Funk Software, CheckPoint, Integic, CISCO, Columbitech, Netilla, Avaya, Evidian, Citrix, Microsoft, NetworkEngines, Novell, Netegrity, Nomadix, Whale Communications, PassGo, Protocom, Sonicwall, Uroam, and many more ...
DIGITKEY Strong Authentication is secure solution but not difficult to integrate at all. Thanks to the DIGITKEY Controller server which is a C-Library with C-API or Java-wrapper. It operates on any Operating Systems with any existing server applications. It use your existing Application Client Database. There is no need to upgrade your existing systems at all.
More than 250 Financial Institutions has integrated DIGITKEY Controller for securing e-Banking, phone-banking, e-Brokerage, etc.
2) E-Commerce integration
DIGITKEY authentication solution has already been integrated into 3D-Secure schemes:
3) Remote Access & Corporate Network Access
The DIGITKEY authentication solution has been integrated in Firewalls, VPN, Radius servers, Portal softwares, ... from many Vendors: Netscreen, Lucent Technologies, Stonesoft, Funk Software, CheckPoint, Integic, CISCO, Columbitech, Netilla, Avaya, Evidian, Citrix, Microsoft, NetworkEngines, Novell, Netegrity, Nomadix, Whale Communications, PassGo, Protocom, Sonicwall, Uroam, and many more ...